Enterprise BYOD Infrastructure Risk Report
Uncontrolled BYOD and wireless-first access are pushing enterprise networks beyond architectural limits, impacting performance, security, and scalability.
By Aerohive Networks | Whitepaper | Source: The iEverything Enterprise
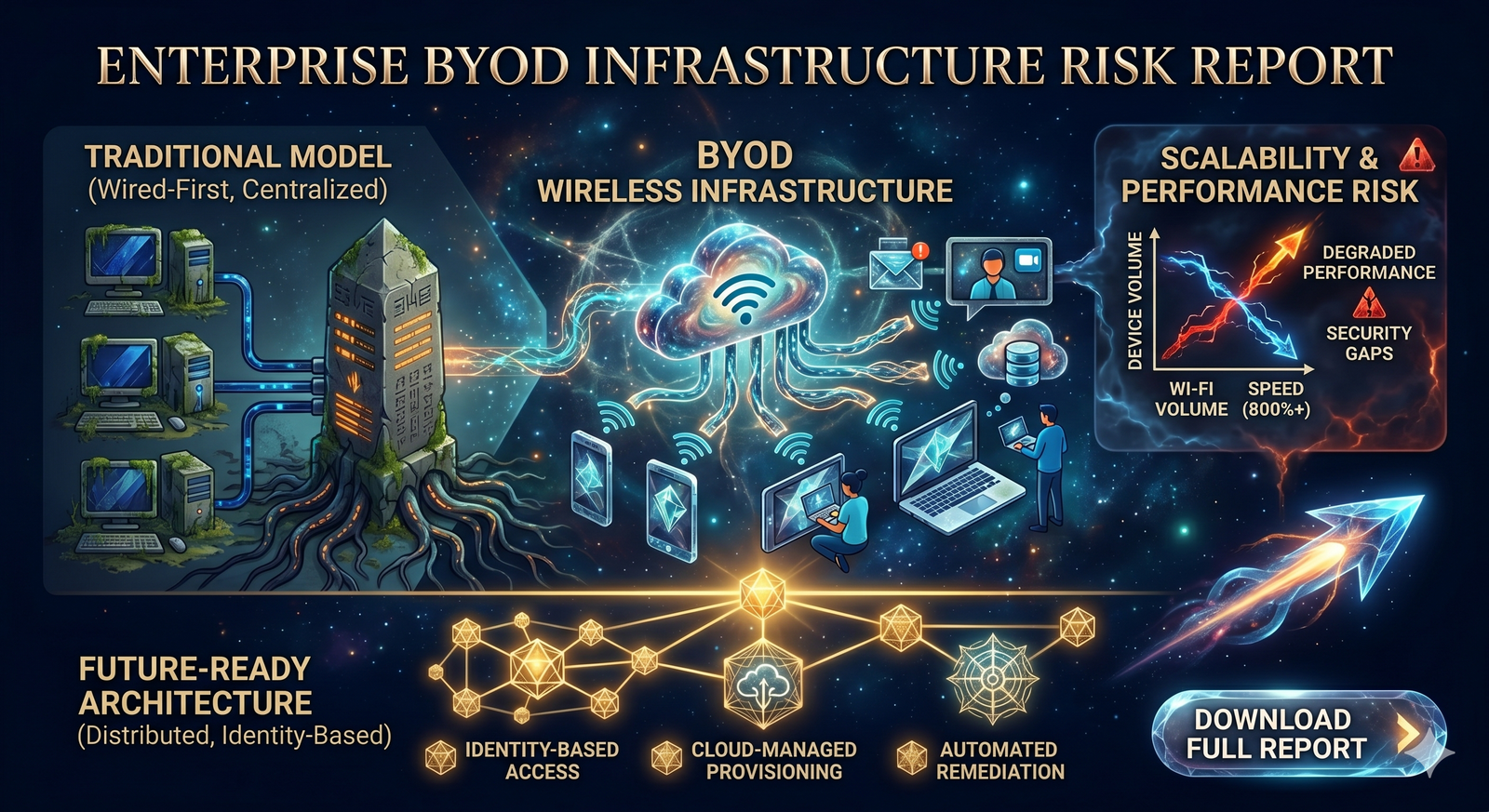
Enterprise IT has shifted from wired-first environments to mobile, cloud-driven access powered by smartphones, tablets, and virtualized applications.This evolution has transformed Wi-Fi into a primary access layer, forcing IT leaders to rethink infrastructure, identity control, and application delivery at scale.Traditional centralized network architectures cannot sustain the scale, speed, and distribution of modern BYOD-driven enterprise environments.
With Wi-Fi speeds increasing over 800% and device volumes rapidly expanding, centralized control models create bottlenecks and limit real-time application performance.⚠ Within the next 2–4 years, enterprises relying on legacy wireless architectures will face degraded application performance, security gaps, and failure to support mission-critical systems across cloud and mobile environments.
For CIOs and infrastructure leaders, this shift directly impacts workforce productivity, cloud application reliability, and enterprise security posture.- Adopt distributed (controller-less) wireless architectures
- Implement identity-based access and policy enforcement
- Leverage cloud-managed network provisioning and control
- Enable real-time network visibility and automated remediation
Enterprise BYOD & Wireless Infrastructure Assessment
Identify scalability limits, security gaps, and performance risks in your wireless-first enterprise environment.✔ Infrastructure risk analysis
✔ BYOD policy alignment review
✔ Network scalability assessment
✔ Architecture modernization roadmap
Download Full Report