AI Security Readiness Report

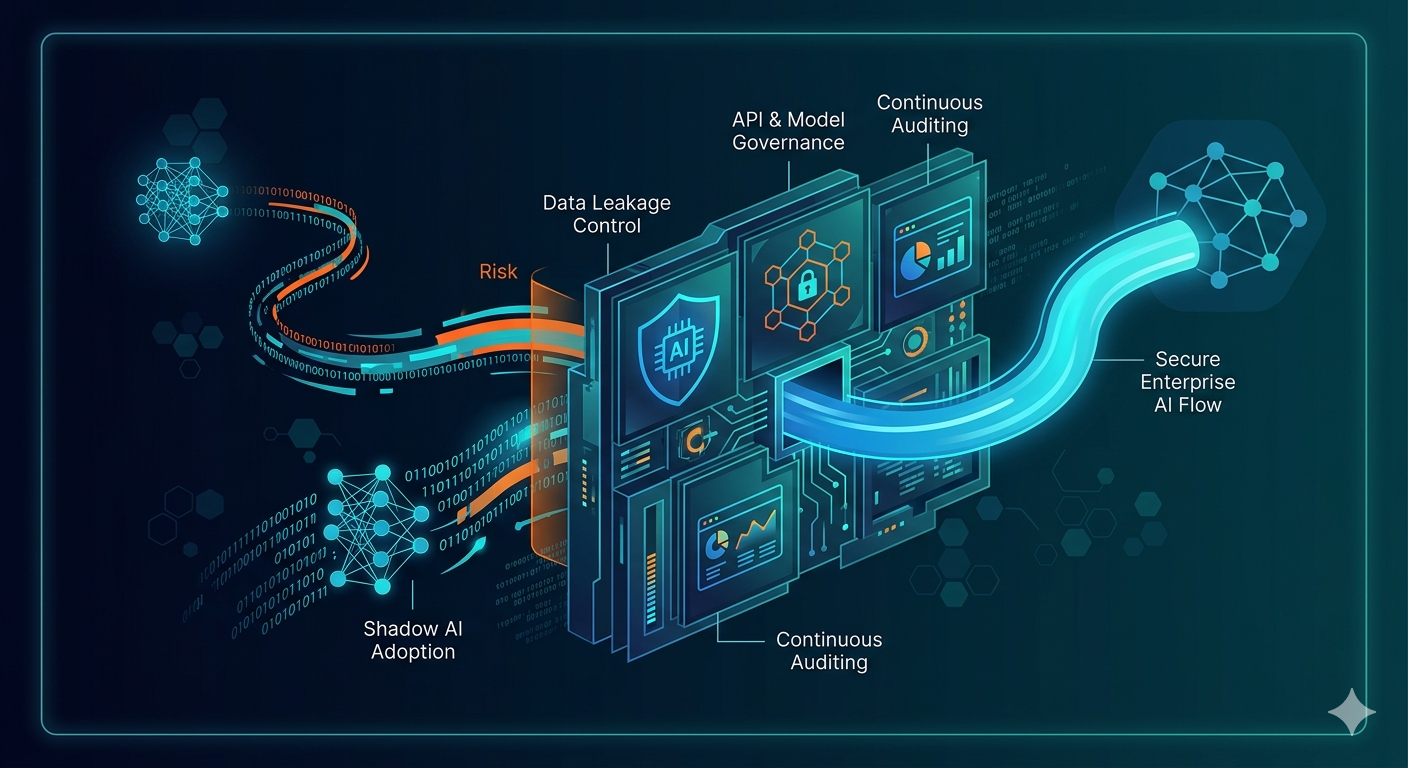
AI adoption is accelerating faster than governance, exposing enterprises to shadow usage, data leakage, and unmanaged model risk.
By Cato Networks | Strategic Guide | Source: Cato
Most enterprises begin AI adoption through employee-led tools before security oversight is in place.
That early convenience quickly shifts into board-level risk as AI moves into apps, workflows, and customer operations.
Without visibility into sanctioned and unsanctioned AI use, CISOs cannot control enterprise exposure or prove governance.
Security leaders now need controls across prompts, APIs, models, identities, and third-party AI vendors—not just endpoints.
⚠ Within the next 12 months, unmanaged AI use can trigger compliance breaches, IP loss, and production disruptions across cloud and business systems.
Leading enterprises are treating AI security as an operating model built on Zero Trust, SASE, and continuous monitoring.
- Discover shadow AI across users and traffic
- Apply identity and least-privilege controls
- Scan models, APIs, and supply chains
- Audit prompts, outputs, and sensitive data flows
This approach protects innovation speed while giving executive teams measurable control, resilience, and audit readiness.
Enterprise AI Exposure Intelligence Brief
Benchmark your AI risk posture and prioritize the controls needed for secure enterprise-scale adoption.
✔ Shadow AI visibility gaps
✔ Governance maturity score
✔ Risk reduction roadmap
✔ Executive action priorities
Download the Report✔ Shadow AI visibility gaps
✔ Governance maturity score
✔ Risk reduction roadmap
✔ Executive action priorities
